This story is from Texas Monthly’s archives. We have left the text as it was originally published to maintain a clear historical record. Read more here about our archive digitization project.
Out past Elgin, off U.S. 290, is an unmarked red-clay road. Off that road is another that leads up and down steep hills to an opening in a stand of trees. From there a winding path sneaks through the forest and dead-ends at a rambling house that sits behind a semicircle of half a dozen cars and trucks, most of which seem beyond repair.
Peter Banz, splattered with red clay, gray clay, and sand, is working behind the house. He has spent the day on a front-end loader and produced a large, deep hole; he put a plastic swimming pool in the hole and filled it with water. He calls it a fish pond, but it looks like a mud pit. “It needs some work,” he says. He trudges back to the house, stopping off at his office before heading for the shower.
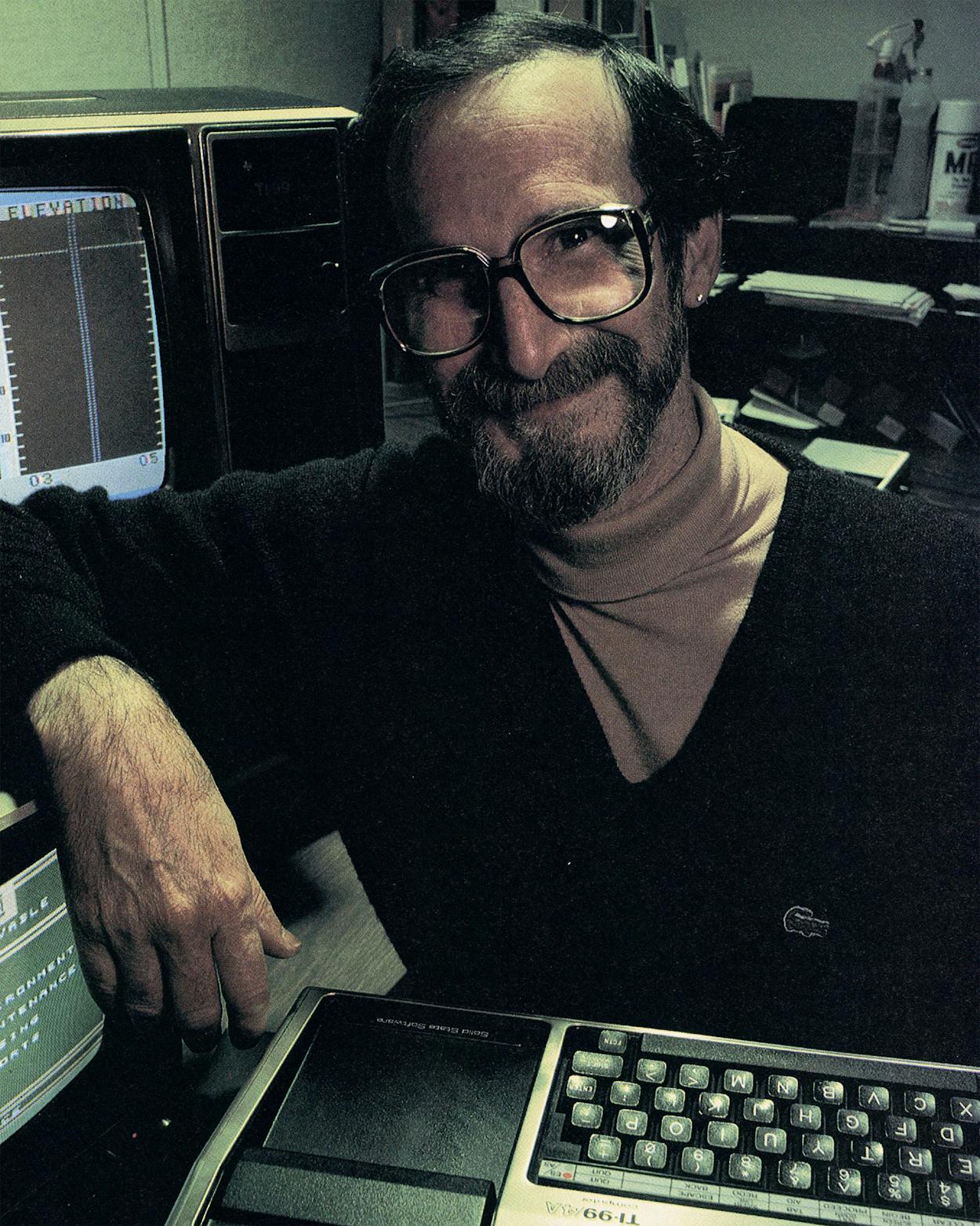
A narrow pathway has been cleared through the clutter in his office. Most prominent is the electronics clutter: keyboards and small buckets full of chips that Banz uses to fix and expand computers sent to him by friends and friends of friends, printers clacking out the most recent draft of an instruction book for his new mailing-list program, and streams of cable meandering under chairs and over boxes of fanfold paper. Three Radio Shack computers—an ancient (pre-1980) Model I and two Color Computers—are set up in the room. One of the Color Computers is unplugged and in need of repair; the other is busy displaying color graphics. National magazines devoted solely to the CoCo (as the Color Computer is affectionately known to users) are scattered around—Color Computer Magazine, Color Computer News, Rainbow, Color Computer Weekly, and Hot CoCo.
Not everything in the office is related to computers, though. Banz’s company, Ceratec, encompasses both his computer activities and a brick-making business that he runs from his home. The latter enterprise contributes more clutter to the office: opened and unopened mail, catalogs, printouts draped between the desk and tables, and piles of receipts and invoices.
The phone rings once and then stops, although no one has answered it. Various machines in the room whine, churn, and click into action. Caller number 5792 logs on, and the words “the Avenger Cedar Rapids IA,” identifying him, appear for a second on the screen of the Model I. They are replaced by a portrait of Banz’s cat, Morris, who wears a brightly colored hat and drives a shiny red car across the screen. Morris welcomes the Avenger. Banz laughs about the picture, explaining that he’s had a lot of fun outfitting Morris with the hat, the little car, even a Santa Claus suit at Christmas. “I like to introduce a little humor into this. Otherwise, people get too serious,” he says.
After Morris drives away, a long list of selections appears. The Avenger can choose from twenty or so offerings, such as Graphics Contest, Editorials, Bargain Mart, and Texas Landmarks. The list remains on the screen until the Avenger, more than a thousand miles away, makes up his mind.
Peter Banz is the sysop of a CoCo BBS. That is, he is the systems operator of a Color Computer bulletin board service. The service provides Banz and his fellow CoCo owners with a center for communication; through it they share information and advice, leave messages for each other, and call up files of graphics, software reviews, and other items of interest that Banz makes available. Unlike some larger, more commercial services, Banz’s BBS has no membership requirements and does not charge callers subscription or access fees. Anyone with a Radio Shack Color Computer and a modem—a device that enables computers to communicate over telephone lines—can use his service; the only cost is that of a long distance telephone call to Elgin. The out-of-pocket expenses of running such a service are minimal—just a few dollars extra on his electric bill and the cost of business phone lines. The time and equipment needed to maintain it around the clock, however, are substantial. Devoting his CoCo to a bulletin board service essentially makes it public property.
Why would anyone dedicate himself and his computer to a BBS? Much of Banz’s motivation comes from a feeling that he is participating in the future. Now 31, he came to Texas from Switzerland in 1977 to work for Elgin-Butler as a brick-manufacturing specialist. Not until 1980, when he began to use a friend’s computer, did he become intrigued by bulletin board services. He tapped into every one he could find, and he says his phone bill was soon up to four figures. Finally he decided to establish his own service. He is proud to have started the second Color Computer BBS in existence, just a few months after the first one, which is in New York City. He dominated the graphics aspect of the field for more than a year, until others sprang up throughout the country. Today there are around seventy Color Computer bulletin boards, and every few weeks Banz hears of a new one. Texas now has about six.
The popularity of these services partly stems from the success enjoyed by the Color Computer itself. The CoCo is manufactured in Fort Worth by Tandy Radio Shack, and since its introduction in 1980, it has won a loyal, perhaps even fanatic, following in Texas. The Henderson Color Computer Club, one of the first CoCo clubs in the country, was founded in January 1982. So many people joined the club that within months of its founding, it became the East Texas Color Computer Club. A year later the club had 1500 more new members from all over the world, and in a full-page ad in the January 1983 edition of Rainbow, it announced that it had a new name, the International Color Computer Club, and proclaimed itself the world’s largest CoCo club. It distributes its own newsletter, helps its members exchange programs, and offers discounts on CoCo merchandise.
Tandy, traditionally a close-knit, secretive company, refuses to reveal the number of Color Computers it has sold. A representative of the company would say only that there are “a heck of a lot of them out there.” Last year the president of the International Color Computer Club estimated that more than 300,000 had been sold. I asked a Radio Shack executive if that figure was correct. He was unwilling to say anything, but he nodded his head affirmatively. I tried 400,000. He nodded again. I jumped directly to a million. Again a nod. I tried two million. The game was over; he just smiled.
Banz calculates that about three hundred CoCo owners use his BBS each month. Often they report the offerings of other BBSs to Banz’s message center, where the information can then be read by other callers. Callers sometimes leave information about “pirate” BBSs. (Such a service may list, for instance, the phone numbers and security codes needed to get into the computers of Exxon and Visa.) Some BBS specialties include vivid sexual graffiti, Yankee jokes, reviews of science fiction films, and the phone numbers of other BBSs.
Banz modestly points out that his service has one of the largest selections of color graphics for CoCos in the world. His pictures have established his bulletin board’s reputation as one well worth the cost of a phone call, and its users log in from all over the country. In Texas, Banz’s biggest markets are Austin, Corpus Christi, Baytown, Houston, and Dallas, with strong showings from El Paso and Midland. It is not unusual for a caller to spend several hours meandering through the various portions of the BBS.
As Banz talks, the computer again begins to whir. The Avenger has made his selection, and within seconds panoramic views of Texas appear on his screen and ours. The file includes the Alamo, the LBJ Library, and a breathtaking Houston skyline, each accompanied by a short historical note. Banz hopes to portray the Battle of the Alamo in the future, but so far he hasn’t been able to depict it with the detail necessary to meet his rigorous standards.
His computer is not at fault.
The rate at which data can be transmitted over phone lines by using a modem is limited, and even with a fancier computer it would not be practical to send a more detailed picture. Banz draws his pictures on a grid that allows him 64 pixels (“picture elements,” or dots of light) across, 32 pixels down, and eight colors; it takes a little more than thirteen seconds for a complete picture to appear on the screen. The Color Computer can give him much higher resolution—up to 256 pixels across and 192 pixels down, with two colors—but it would take nearly three minutes for a picture to be displayed on the screen. Few users want to wait and pay for all that long distance time. Given today’s limitations, Banz’s graphics cannot be outdone. He is currently in the process of transferring his graphics from the Model I, which has completely broken down, to his Color Computer.
When not scrolling through the graphics displays, the average user spends much of his time within the magazine portion of the BBS, all of which is written by Banz. Like a printed magazine, it has regular departments and features, editorials, the latest rumors in the computer world, and reviews of new products, including what Banz refers to as “the Monkey King Kong Dong Games” and “the Pac Smac Mac Bunch.” Banz can find out exactly how many times each viewer calls in (anywhere from daily to three or four times a month), how frequently an article is requested, and how much of it gets read.
Too often these figures indicate that it is time for fresh material. Every month or so Banz spends long hours testing new products, writing new articles, and drawing new pictures. The failure of most sysops to update their services explains why many of them fold within their first few weeks of operation. Users do not return to read stale news.
The BBS consumes Banz’s time in still another way—through the chat mode. The user types in his end of the conversation, which appears on Banz’s screen; Banz then types in his reply, which appears on the user’s screen. A conversation can continue in this way for hours. As the sysop, Banz is duty-bound to chat for as long as the user wants.
Soon the avenger signs off. His twenty minutes on the BBS will show up as a $4 to $5 charge on his next phone bill. Because this was the avenger’s first call and because he used a pseudonym, Banz monitored his activities carefully. The computer world, like any other, has its share of troublemakers. Most people who abuse BBSs commit only minor breaches of etiquette, such as crowding a board with repeated pronouncements. Others exhibit rather disturbing behavior. Users have been known to leave suicidal messages on a dozen BBSs at the same time, begging anyone who signs on to become a friend. Lewd language often blips across the screen. And then there are system zappers, users who try to destroy the BBS program itself.
To combat such problems, sysops are beginning to install various levels of security. In the program that Banz sells to people starting their own BBSs, not all message boards and services are open to every caller; some require a password for entry and allow users to leave messages for the sysop that no other user can read. One section, to which no user normally has access, monitors the entire system. But to a system zapper, security codes exist only to be broken. A malicious zapper can hopelessly garble the software needed to run the BBS. It may take the sysop as much as two months to put all the pieces back together more securely. And there is still no guarantee that a zapper won’t strike again.
While Banz and I are talking, another user logs on and requests the graphics file. But this time something goes wrong; gaining access to Banz’s wonderful pictures has become impossible. Banz, instantly obsessed, searches through several feet of computer listings for the error. It turns out that something called the H file, crucial for the graphics display, is missing. He pushes a few buttons, trying for a quick fix, but the H file is not so easily resurrected. He searches the office frantically for the H file printout so he can reenter it into the system. At first he blames his wife for losing the printout; when he finds it, he blames Morris for covering it with paw prints; he is ready to blame me for something, until I remind him about the system zapper. Finally he blames himself. He has recently increased the program’s security, and in the process the H file was deleted. He mutters that at least he is in Texas and not New York, where telecommunications vandalism is much more common.
Banz is barely able to keep up with the constant attention that his BBS demands. A computer system that runs 24 hours a day does not run smoothly for very long at a time, and when repairs are needed, they must be made immediately. Banz cannot afford to wait weeks for a Radio Shack store to fix his computer; callers would assume that his service had folded. So he does his own maintenance. Running a BBS and operating as a full-time “hacker”—someone who modifies and extends his computer—are nearly one and the same job.
Users often leave messages on Banz’s BBS requesting help in modifying their Color Computers. He has become known as a specialist in physically transforming the Color Computer, which was intended primarily for games and educational programs, into a more sophisticated tool. A desperate person may resort to telephoning him directly—a “voice call”—asking for instructions. Often the person ends up bringing his computer to Banz, who for a modest fee will take it apart and expand it.
The first step is to turn the computer on its back and remove seven screws from the case. The last screw is covered by a sticker that reads, “Opening case will void warranty.” That warning symbolizes Radio Shack’s attitude toward hackers: proceed at your own risk. In the old days, before the turn of the decade, Radio Shack would not tolerate hardware modifications. When an owner brought in his computer for servicing, Radio Shack would remove all “alien” components and return it in pristine condition.
Taking an entirely different view, Apple built room for eight additional boards of microchips into the IIe computer so that its capabilities could be expanded. Apple also encouraged outsiders to invent and manufacture extensions and modifications. In Banz’s opinion, that attitude is what kept Apple competitive with Radio Shack in the late seventies, despite Radio Shack’s powerful national network of retail stores. Though it was harder to find an Apple, the lack of a warning sticker made it worth the trouble. The IBM Personal Computer, which has five expansion slots, stands as an endorsement of the Apple philosophy: owners have the right to define, and develop their machines. Radio Shack has finally come around to some extent—its new Model 2000 has spaces for four more boards—but it still discourages experimentation.
This afternoon Banz is upgrading a CoCo belonging to a BBS user. Having opened the case to reveal the multicolored chips, capacitors, and resistors within, he next replaces Radio Shack’s inferior, “Chiclet”-style keyboard with a sleek new one, similar to that on an electric typewriter. Choosing the right keyboard is important, since it is a user’s main way of communicating with his computer. The lowest form is the membrane keyboard, a pressure-sensitive panel used widely in microwave ovens and copying machines. The bottom-of-the-line Atari and the initial version of the Timex/Sinclair computer have this kind of keyboard. It is easy to clean and requires no maintenance, but entering any significant amount of data with it is difficult. The next step up in keyboards features little square Chiclets as keys, like those commonly found on calculators. Until recently the CoCo had that type of keyboard; it now comes with a touch-typing keyboard that Banz describes as “toylike.” Five companies make superior replacement keyboards like the one Banz is now installing.
Next, Banz pops out the computer’s eight memory chips. A computer’s memory—defined by the amount of data it can juggle and store on a temporary basis—determines the complexity of the programs that can be run. A small memory can severely limit the usefulness of a machine. These chips can each store 16,384, or 16K, bits (pieces of information). That’s plenty of room for a decent game but not enough for applications like word processing, which require additional memory space for storage of data created by the program. With 16K bits, only about five to six pages of text would be possible. Banz will charge the computer’s owner about $50 to replace the eight 16K chips with 64K chips, bringing the Color Computer to its maximum configuration. It takes him about a minute.
In addition to tinkering with hardware and running his BBS, Banz has begun to write and market software for the Color Computer. Every time his BBS has crashed, whether because of system zappers or lightning bolts, he has improved it as he reconstructed it. Would-be sysops purchase programs from him that allow them to turn their own computers into BBSs; a recent sale was to a BBS starting up in El Paso, the fourth in that city. He has also toyed with writing business software for the CoCo, including his complex mailing-list program.
Once a hacker becomes a businessman, though, computer expertise alone is not enough for success. The computer industry is a frenetic, high-risk business, and changing technology repeatedly renders yesterday’s innovation obsolete. Software vendors often spend an extraordinarily high $1 in advertising for every $2 of sales. For now, Banz is content to sell his software through his BBS. It doesn’t cost him anything, and to some extent it justifies operating his BBS. Besides, he can write his own rave reviews.
The Software Cowboy
Software piracy is perhaps the most discouraging problem facing computer entrepreneurs. Like songs, poems, plays, and novels, computer programs enjoy copyright protection, and once purchased they are intended only for the personal use of the owner. Piracy, however, runs rampant. Making an illicit copy of an unprotected program requires only inserting the program and a blank disk into the computer, punching some buttons, and waiting a few seconds for the program to be duplicated. Most makers of software therefore build some form of copy protection into their programs. For example, a program may fool the computer into thinking that there is an error in the copy, which causes the computer to abort it. But the more intricate the protection scheme, the more the software pirates rise to the challenge. They pounce on each new copy-protected program, defiantly slash through its security layers, then sell illegally made copies at greatly reduced prices. A common estimate is that for every program sold, nineteen are stolen.
At the center of the piracy controversy is Kim Watt, 30, an ace programmer for the Dallas-based software company PowerSoft. Most who know of him agree he is a genius. His programs have often been voted the best in polls taken by computer magazines. His most popular program, Super Utility Plus, is a powerful piece of software for Radio Shack’s TRS-80 Models I, III, and 4 that makes it far easier to perform usually complicated functions—including stealing programs. Those who have benefited from Super Utility Plus see Kim Watt riding across the computer frontier in gleaming white; those programmers who suspect that Super Utility Plus has been used to steal their creations see only a villain in black.
Much of Watt’s software simplifies the creation of other, more complex programs. Suppose, for instance, that a programmer working on a game wants an animated effect. Figuring out the best method of getting it might take several hours or days of experimentation if he starts from scratch. But if he uses Watt’s program PowerDraw, it becomes dramatically easier to draw the individual screens and to combine them for an animated effect. All this for $39.95.
Even novice users find Watt’s programs extremely helpful. Many people know that untapped power lies within their machines but are afraid to venture out on their own. Watt expands their horizons, blazing well-marked trails through the difficult inner terrain of their computers. His programs give owners a much broader understanding of their machines’ capabilities than do the canned programs from Radio Shack and other entrepreneurs. And Watt’s software can be modified to run on almost all Tandy computers.
To underscore his reputation as a renegade guide through the wilderness of home computing, Watt has wholeheartedly adopted the role of Software Cowboy. It is not unusual to find him at computer shows throughout the country, dressed in a ten-gallon hat and boots, signing autographs and counseling his followers. Though he is originally from Michigan, he looks the part. He has steel-blue eyes, disheveled hair, and a serpentine tattoo on each bicep. His demeanor is also on target; the strong, silent type, he is wary about discussing his work. His comments and answers are clipped and guarded, expressed in a quiet monotone.
He is a college dropout, as are most of the half-dozen people who work for PowerSoft. He was a premed student when he bought his first computer, a TRS-80 Model I, in 1978. Over the next year he built up a software consulting business and found that he could make a comfortable living at it. He delved deeper and deeper into the computer, discovering and documenting routines that no one else had mastered, not even the technicians who designed the machine.
Watt has a genius for circulating thousands of computer instructions in his mind, organized and departmentalized, and for accessing any one of them without effort. His approach to programming has always been unorthodox; as if to spite all the textbooks on the subject, he never constructs a flowchart to outline a program. He just sits down and writes it.
Of the thirty programs that Watt has mounted on the wall of his office, Super Utility Plus has the most prominent position. When it was first put on the market, in 1980, it was the most extensive program written for the TRS-80 Model I and Model III, and PowerSoft sold thousands of copies at $75 apiece. Super Utility Plus, which has been upgraded nine times, is a conglomerate of more than eighty programs designed to make Radio Shack computers more useful to the average owner. For instance, electrical surges sometimes cause a computer to garble data. Using the disk-repair function of Super Utility Plus, most of the data can be recovered, saving hours of reconstruction time.
Unfortunately, the program’s power and desirability are causing problems for PowerSoft. A company once advertised a product whose sole purpose was to make illicit copies of Super Utility Plus; ironically, the techniques used were probably learned from Super Utility Plus. So far no one has managed to break through all the layers of secrecy with which Watt has cloaked its most recent upgrading, but previous versions were pirated, putting a dent in PowerSoft’s profits.
The advanced capabilities of the program have intensified one of the hottest ethical dilemmas for computer owners—to pirate or not to pirate. Everyone in the computer world is eager to give his opinion on the issue, including Banz. He argues that piracy is sometimes justified. He says he has thrown away so much money on bad software—“stuff that doesn’t work and isn’t worth the disk it comes on”—that he now sometimes steals programs just to try them out. “Then, if the program is good and it tells me what it does and I really use it, I don’t want to see them going under, so I buy it,” Banz says. Few users are honest enough to buy a program they’ve already stolen, however. So, to recoup losses from stolen copies, software houses raise their prices; people feel more justified in stealing the overpriced program and do so; the company raises the program’s price once again.
Tracking down software pirates is a complicated business. No practical method exists for tracking the thousands of copies that are illegally made and sold. Mark Davidsaver, a CoCo buff who operates a software company in his home in Austin, complains of the wasted hours he has spent on inventing techniques to protect his programs. Despite his precautions, within days after he starts selling newly secured software, a pirate in Southern California always broadcasts a method to crack its protection on bulletin board services throughout the country.
In a letters-to-the-editor column that one computer magazine devoted to the piracy problem, a reader wrote in, “My personal solution is to enclose a picture of my little boy with every program sold. I will also enclose a note begging people not to make illicit copies of the program or I will not be able to feed my little boy.”
Star-Kits, a company that produced software for the Color Computer, took a novel approach to piracy. It offered amnesty to the owners of pirated software if they named their source and paid 25 per cent of the program’s cost. The repentant owner was registered as a bona fide customer and got an up-to-date copy of the program and an accompanying manual. The large response to their offer indicated how pervasive piracy was. As a result, Star-Kits will no longer market programs for the CoCo. Instead, it will concentrate on software for more-expensive machines, in the hopes that those owners will be less likely to pirate programs.
Watt decided that rather than watch his secrets slowly leak away, he would tell all—for a price. In a bold move that shocked the Radio Shack computer world, he wrote a book explaining the inner workings of Super Utility Plus. He published a limited edition of five hundred copies and offered them at $500 each. His marketing manager eulogized the book in an ad in a national computer magazine:
All of Kim’s knowledge in ONE book! . . . It is a collector’s item, also. Limited, Indeed. Last, but not least, it is expensive. On the surface only, however, as this product will make you an expert programmer if that is what you want. . . . It will also make you a member of an elite group that has access to Kim’s knowledge and can USE that knowledge to YOUR benefit.
About two hundred of these almost mystical tomes are still available, but they are disappearing quickly. Owners include several government departments, the Navy, MIT and other universities, and Radio Shack employees. Of course, not even the Lone Ranger can be expected to give away all his silver bullets. Watt points to a stack of computer printouts, almost two feet high, on a bookshelf on the other side of his office. “Couldn’t fit all of it into the book,” he says.
The Veteran
Long-range radar shows an enemy missile bearing 320 degrees and zeroing in on Fort Worth. Charles Ehninger, in charge of the surface-to-air missile defense system, calmly presses a few buttons on the control console, activating the tracking radar. The missile, now twenty miles away, appears on the screen. The enemy is trying one of its most evasive maneuvers, flying low on the horizon, underneath the effective angle of the antimissile system. If the missile gets within ten miles of Fort Worth, it will be invulnerable.
Ehninger runs his fingers through his bushy, graying beard. His gold rings flash—the heavy one on his finger, encircled with the words “UT at Arlington,” and a plain hoop that dangles from his ear.
The screen goes blank. His radar has been jammed. He pushes more buttons, searching for a new radar frequency. After nerve-racking seconds, the missile reappears on the screen but is now only fifteen miles away. The beeps get louder and Ehninger quieter as he concentrates on zooming in on the missile. He finally succeeds in locking the tracking radar onto it, twelve miles from impact. He launches his antimissile missile. It roars into the sky, seeking out its prey. Ehninger smiles, and the wrinkles on his forehead relax. “That should be it. Even if the enemy missile changes its direction, our missile will follow it. Unless . . .” “Unless?”
“Unless it jams our locking frequency.” “Then what?”
Even as he speaks, sirens blast from the control console. The locking frequency has been jammed. Ehninger returns to the keyboard, frantically retreating to manual controls to guide his missile. But his efforts are useless. Fort Worth is obliterated in a cataclysmic shower of light and color.
Playing Surface-to-air Missile (SAM) Defense System obviously gives Ehninger pleasure. One of the first games he wrote for the Texas Instruments home computer, it has become a classic, partly because of its realism. His experience as a war-games programmer for the Pentagon made him unusually qualified to write an authentic “the sky is falling—look out for the nukes” video game.
Ehninger, now 54, began his career in the fifties as a technician for the Army Air Force on a computer called Geniac. Back then, most of the few existing computers belonged to universities and government institutions, and each had its own name. They inhabited environmentally controlled buildings, attended by technicians like Ehninger who dressed in long white coats. To most people, computers were mysterious and a little frightening but definitely exciting. The computer made one of its first public appearances in November 1956, when CBS captured the country’s imagination by televising Remington Rand’s Univac on the night of the presidential election. The “giant brain” performed beautifully, predicting that Eisenhower’s odds of winning were a hundred to one.
The amazed viewers were treated to a mesmerizing display of blinking red, green, and amber lights, rows and rows of buttons clicking on and off, wheels of tape twirling. But it wasn’t the real thing—CBS had built a facsimile of the Univac’s control console. Ehninger, who clearly remembers the excitement of the event, could only dream at the time of owning such a machine. Though he was far more conversant with computers than most Americans were, he could act only as their servant, not as their master.
In the sixties Ehninger went to work for IBM as a systems engineer. But after four years, he tired of using what he felt was less than the best hardware available. He set out on his own, wandering through Texas, programming business computers on a freelance basis. During those years, he installed computers, customized programs, and trained personnel in every major city in Texas. Then, bored with working on other people’s computers, he returned to school to improve upon his sixth-grade education. In three years he finished an undergraduate degree and a master’s degree, both in economics.
While he was in school, the industry advanced. By 1979 it had produced the home computer, bringing a machine of considerable power within the price range of the ordinary individual. Perhaps only a person who had spent most of his life in the industry could feel as thrilled as Ehninger did at the idea of owning a computer. He didn’t hesitate to spend what he considered the ridiculously low price of $1000 for the Texas Instruments home computer. At last he could create his own displays and write programs for his own use. The computer was his.
He chose the Texas Instruments computer partly because he was well acquainted with its microprocessor—the chip that serves as the brain of the computer—and knew the language required to program it. But practicality was not Ehninger’s only criterion. He was intrigued by the computer’s unique ability to draw anything from single points to spaceships and kaleidoscopic designs in a manner that never repeats but is not random. Those “sprites,” designed by the user but with a life of their own, moved at speeds and in directions specified by a program. Ehninger was convinced that no other home computer could touch TI’s.
In the process of toying with the home computer, he wrote what he says was “a simple program with some unique little twists,” which won the first prize of $3000 in a contest sponsored by Texas Instruments. The prize money allowed Ehninger to start his own business in his Fort Worth home. He began by writing games like the SAM Defense System. But soon games were no longer a challenge, as they took him only a few weeks to perfect.
He switched to a more exciting and subversive project: converting the Texas Instruments home computer into an effective tool for corporate executives and independent businessmen. Ehninger produced eight business packages for the TI home computer, from Accounts Payable to General Ledger. He then added a data-storage device that allowed instant access to more than ten million bits of information, enabling small businesses to step into the megabyte world at a fraction of the cost of a personal-computer system.
Ehninger’s programs have done extremely well. In the last year sales have tripled, and more than 150,000 copies of the programs have been sold since he went to work for himself. Over the past five years his business has moved from the bedroom to the den, then to an enclosed patio, and finally to a storefront in a small shopping center. Even though he is still perfecting his software system, he has already sold more than twenty packages, at about $5000 each.
Ehninger enjoys his financial success and the respect that it has earned him in the computer world. He has assumed the role of a senior adviser, lecturing to computer clubs, writing an occasional article, and reviewing game programs sent to him by budding computer wizards. He feeds the newest game he has accepted for distribution, Newton’s Revenge, into the computer. He pushes a key indicating that he wants the highest level of difficulty. A second later an apple tree and a bucket appear on the screen. Apples tumble down from the tree at an alarming rate, and he manipulates the bucket to catch them all. The next onslaught features even more apples, falling still faster. He is glad that a teenager can invent such a simple yet elegant game on his own computer. Ehninger likes playing the game, and he likes making money for both of them.
When Texas Instruments announced that it was giving up on its home computer in the fall of 1983, Ehninger was prepared. He had analyzed each press release as if he were studying Holy Writ and had checked his hunches with inside sources. Still, he had expected that the transition to other computers would be cumbersome and costly. Instead, it has been easy and profitable. As the price of the now extinct computer dropped to a record low, many people rushed to buy. New and old owners turned to Ehninger for programs to replace those that TI would no longer be marketing, creating a huge surge in his sales. He figures that the TI home computer will be alive at least another couple of years. By that time, all of his programs will be reincarnated on five other computers: TI’s Professional and portable Professional, the IBM Personal Computer and Personal Computer Junior, and the TRS-80 Model 2000.
Confident of his programming and marketing skills, Ehninger plans to compete with the big boys. His previous profits may be loose change compared with the earning power of his most recent brainchild, a hardware and software system for builders. It includes job estimating, bidding, cost projection, and, most significant, the calculation and drawing of the builder’s “critical path.”
Ehninger unrolls a huge piece of paper crammed with squares and circles connected by an intricate maze of lines; he describes it as a scheduling tool. A heavy line representing the critical path runs through the maze and shows the builder the importance and order of the various steps in his construction project. Any event on the critical path can, if delayed, cause the entire project to suffer; events not on the critical path are less important. A builder can look at the critical path and figure out what he needs to do next.
Working with architects and construction companies, Ehninger has automated the process of determining the path; it takes only 45 minutes on the computer, as compared with a week by hand. Information used for calculating the path also feeds into the builder’s business programs, reporting on costs and figuring the payroll. Nothing like it has been written for home or personal computers, though much larger computers, starting at about $50,000, can run a comparable program.
If this latest project takes off, Ehninger could become a millionaire. After 25 years of watching computer companies rise and fall—mostly rise—he may finally share fully in their success. The prospect of continued financial reward is sweet, but to Ehninger it represents the fulfillment of the computer’s potential as much as his own. He believes that computers should not be monopolized by the government and giant businesses, as they once were; they should be used by entrepreneurs to make fortunes for themselves.
He suggests that we attempt to bring Fort Worth back from the grave by playing SAM Defense System one more time. The program is loaded in an instant. The missile appears high in the sky, almost at twelve o’clock. Just before the radar can pick it up, Ehninger loses control of Channel A, and the missile disappears from the screen. He quickly switches to Channel B. The enemy missile is again sighted, now only seventeen miles away.
“This time,” he says, “we’ve got it.”
David Kramer is a freelance writer and attorney who lives in Austin.
- More About:
- TM Classics
- Longreads